What you’ll learn
- How to register a GitLab OAuth Application on your own instance
- How to connect TestDino to a self-managed GitLab via OAuth
- How to link a project and enable MR and commit comments
- How to manage, switch, or disconnect the self-managed connection
https://gitlab.mycompany.com.
After connection, TestDino posts AI test summaries on merge requests and commits to the connected GitLab repository, and keeps MR state in sync with TestDino for Pull Request.
What the Self-Managed Integration Does
- Secure OAuth Login: connects TestDino to the GitLab instance securely, no personal access tokens or shared service accounts.
- MR and Commit Comments: posts AI test summaries with test status metrics, failure summaries, and a link to the full report.
- Automatic Token Refresh: refreshes OAuth tokens in the background so the session stays alive.
Prerequisites
- GitLab instance URL: reachable over HTTPS from TestDino’s servers with a valid TLS certificate, for example
https://gitlab.mycompany.com. - Permission to create an Gitlab OAuth Application: a user-level app on the GitLab account, or a group or instance-level app registered by a GitLab admin.
- Admin role in TestDino: only TestDino project admins can connect or disconnect integrations.
Connect TestDino with Self-Managed GitLab
Connection takes the following steps:- Register an OAuth Application on the GitLab instance
- Provide GitLab Instance URL and OAuth Credentials to TestDino
- Authorize TestDino via GitLab
- Select the GitLab project to connect with TestDino
1. Create a GitLab OAuth Application
In the self-managed GitLab, create a new OAuth application that TestDino uses to sign users in.- Go to User Settings → Applications, or Admin Area → Applications for an instance-wide app.
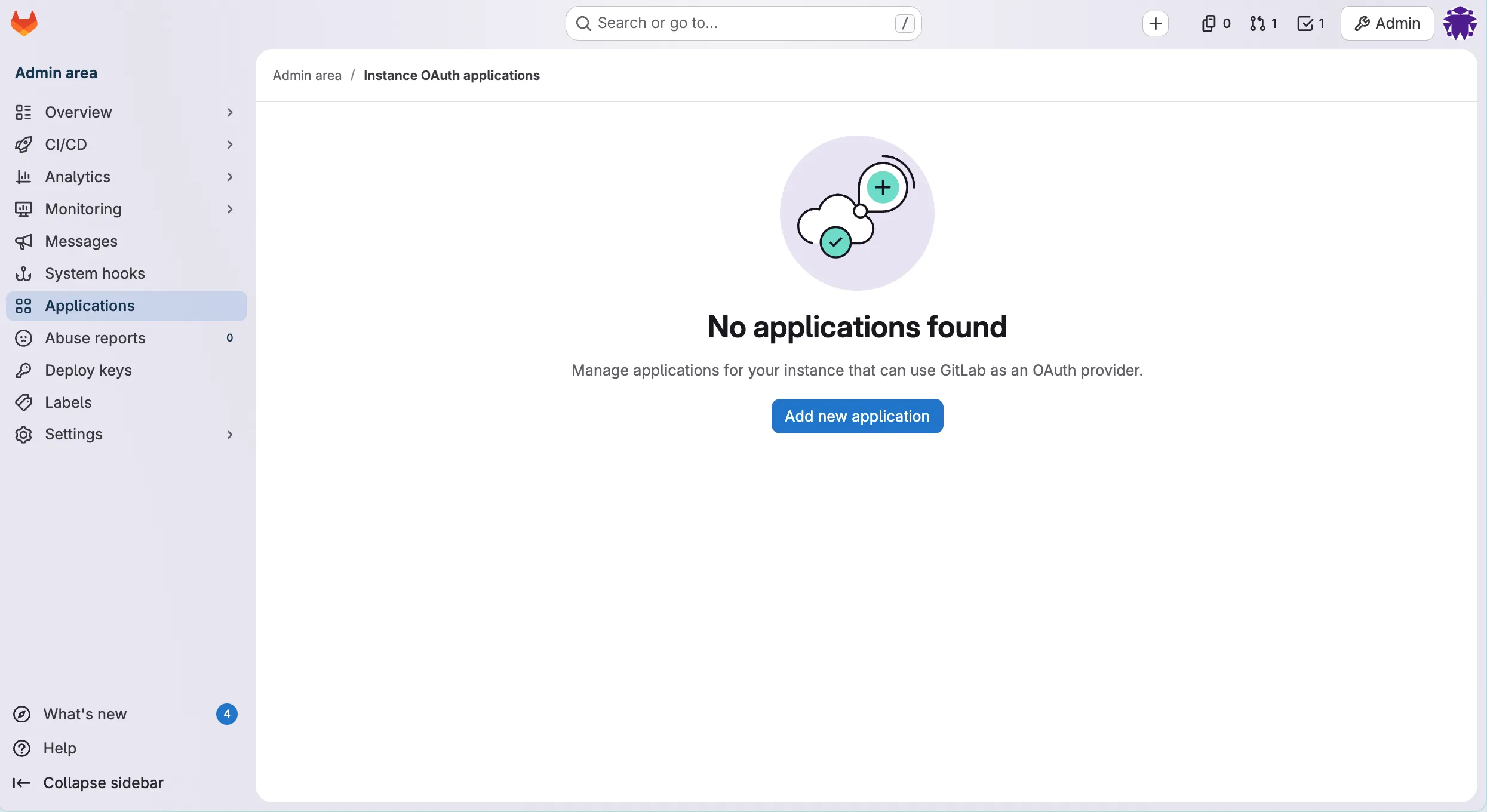
- Click Add new application and fill in the fields below:
| Field | Value |
|---|---|
| Name | TestDino |
| Redirect URI | https://app.testdino.com/api/integrations/gitlab/oauth/callback |
| Confidential | Checked |
| Scopes | api, read_user, read_repository, write_repository |
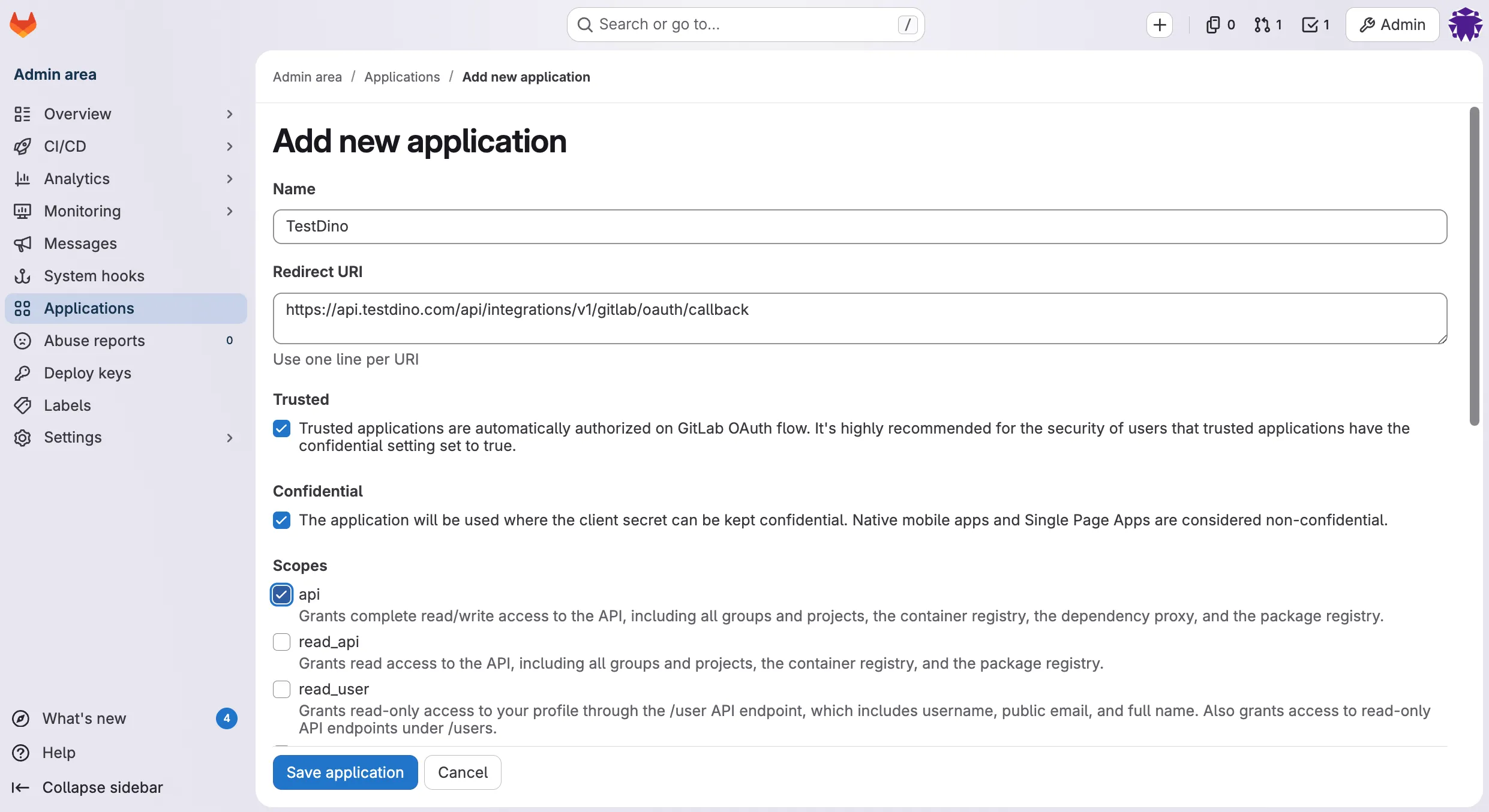
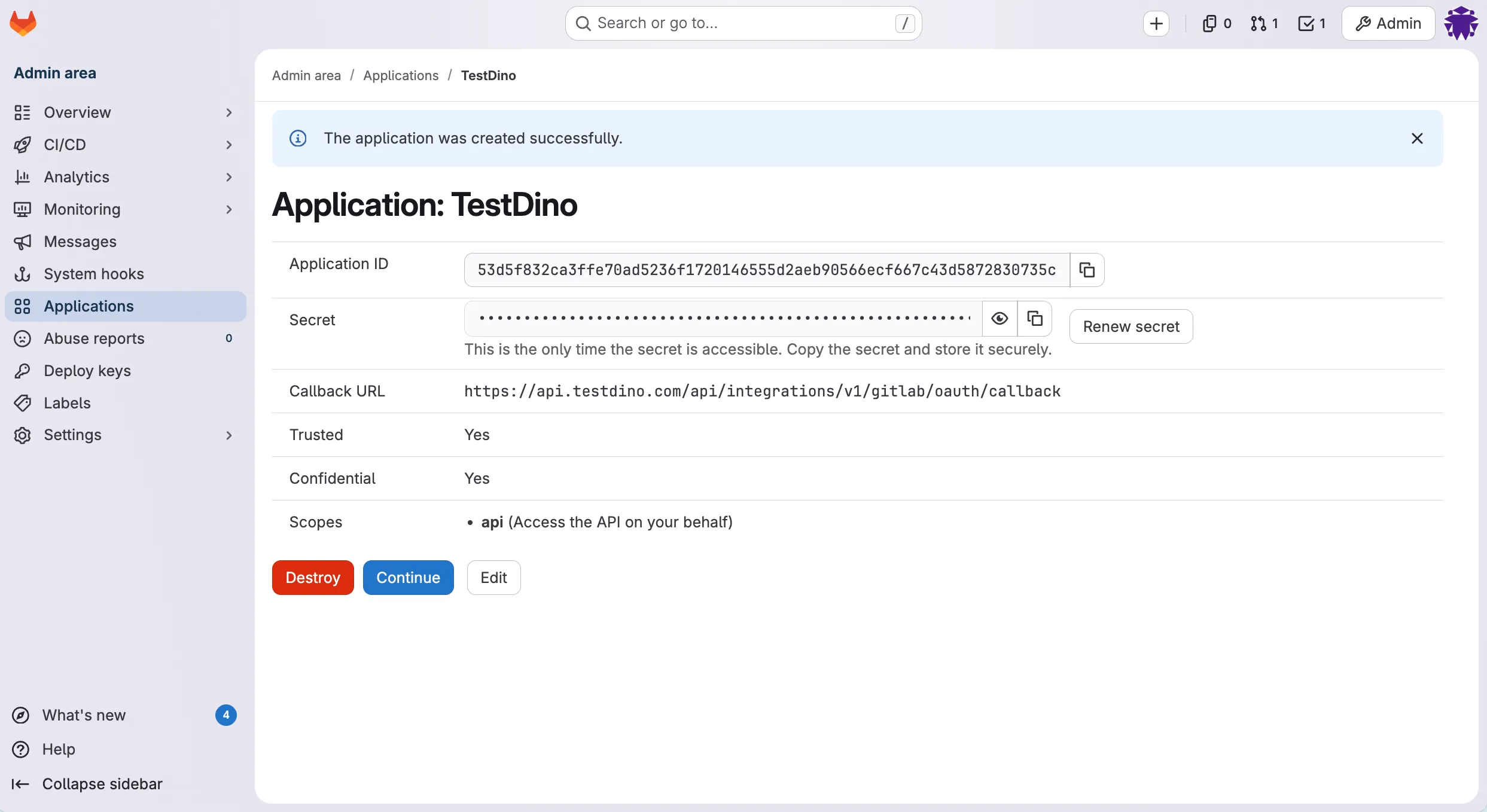
- Click Save application. GitLab shows two values: Application ID and Secret. Keep this page open for the next step.
2. Enter GitLab URL and OAuth Credentials
- In TestDino, open the project and navigate to Project Settings → Integrations → GitLab.
- Click the Connect to GitLab button and choose Connect to GitLab Self-Managed from the dropdown (the option with the server icon).
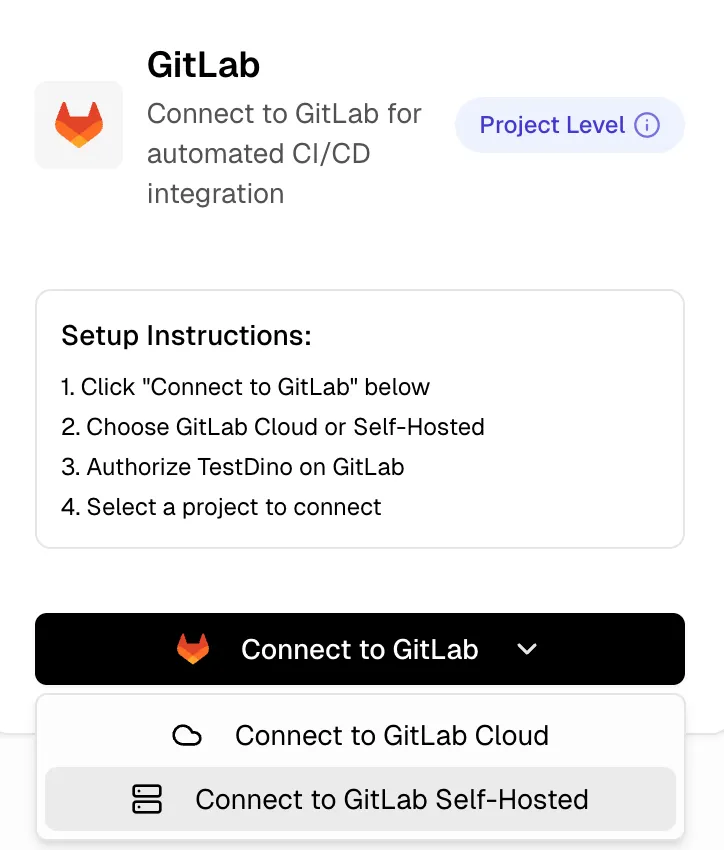
- A dialog titled Connect GitLab Self-Managed opens. Fill in the three values and click Connect:
| Field | What to enter |
|---|---|
| Instance URL | Base URL of the GitLab instance, for example https://gitlab.mycompany.com. No trailing slash, no /api/v4. |
| Application ID | The Application ID from Step 1. |
| Application Secret | The Secret from Step 1. |
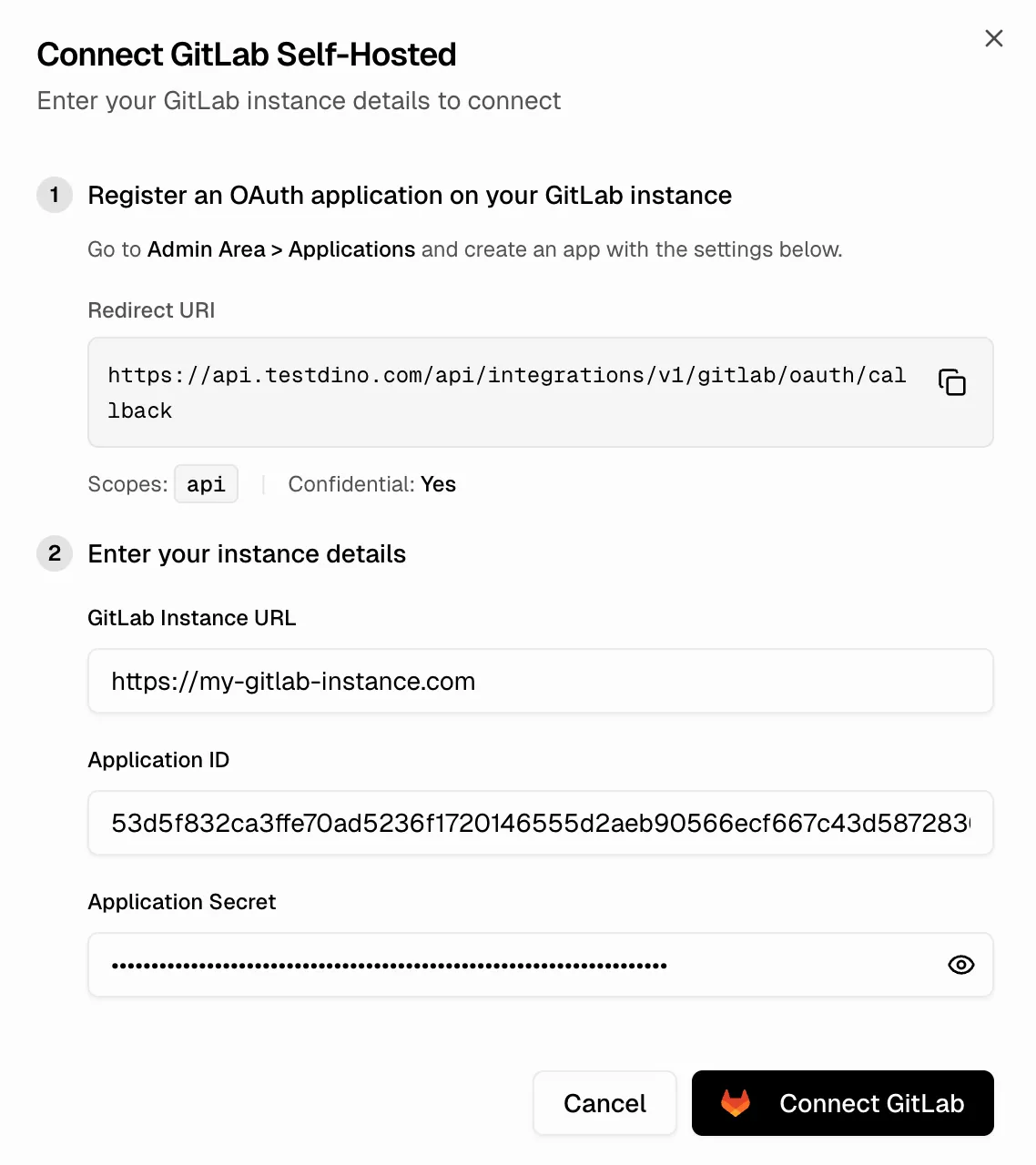 TestDino validates the URL and credentials, then redirects you to the GitLab login and authorization page.
TestDino validates the URL and credentials, then redirects you to the GitLab login and authorization page.
3. Authorize TestDino in your GitLab
- Sign in to GitLab if you are not already signed in.
- GitLab shows an Authorize TestDino consent screen listing the requested scopes.
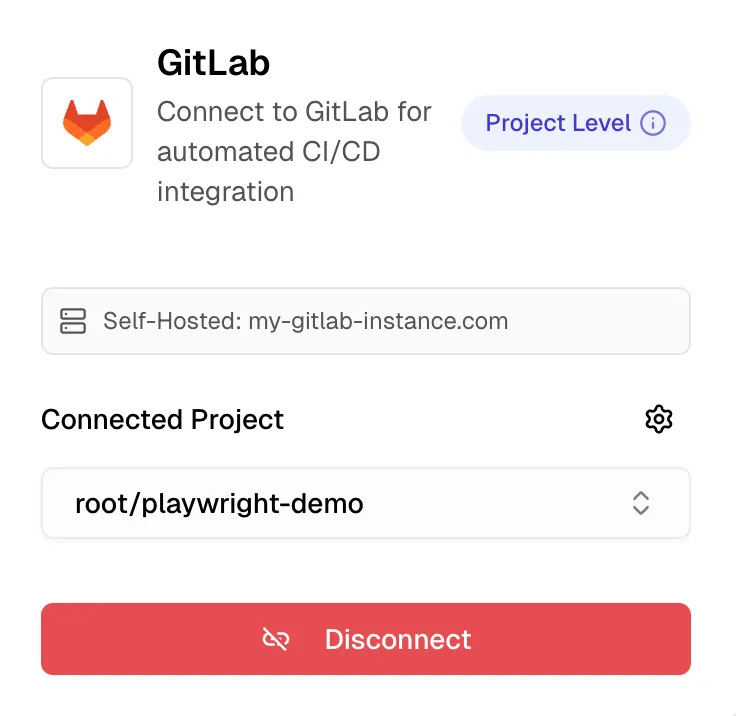
- Click Authorize. You are redirected back to TestDino, and the GitLab card now shows Connected instance URL.
4. Select the GitLab project to link
- On the same GitLab card, a Select GitLab Project picker appears.
- Start typing the project name or group. The list loads from your GitLab instance, not from
gitlab.com. - Pick the project this TestDino project should mirror.
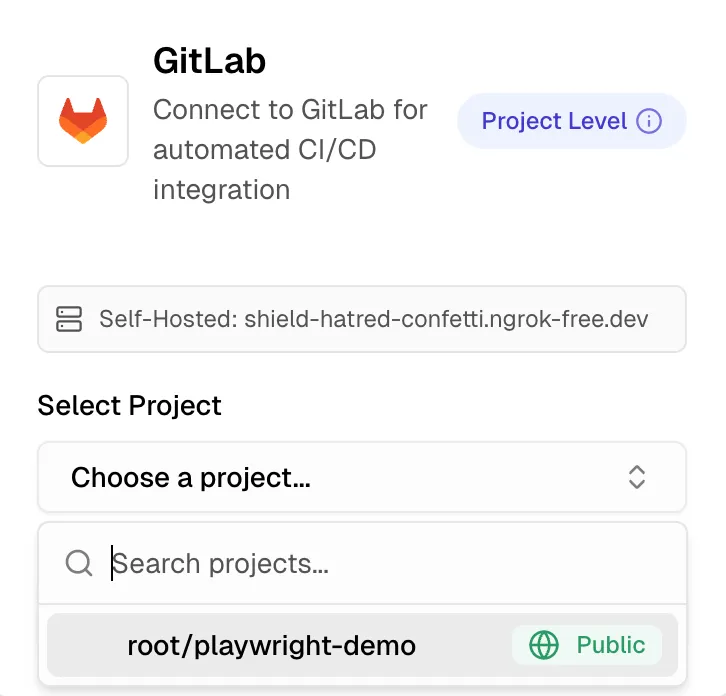
NoteThe picker lists only projects where the connecting user (the GitLab account that authorized TestDino via OAuth) has Developer access or above for projects. Lower-access projects for this user are hidden.
After a successful connection, the integration unlocks MR comments, commit summaries, and comment behavior overrides. Configure each below.
Configure MR and Commit Comments
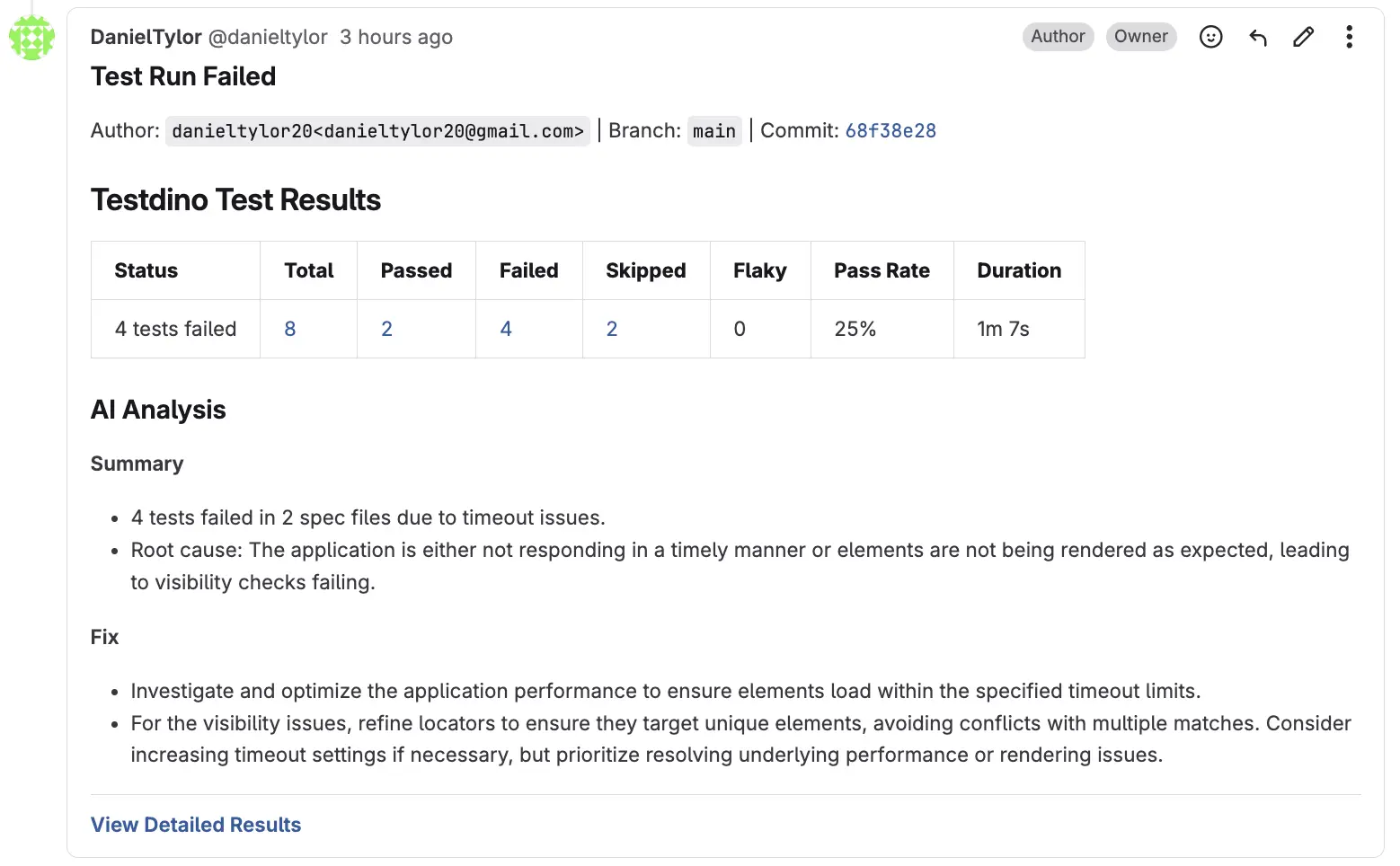 When a Playwright run finishes, TestDino posts an AI-generated summary to the merge request or commit inside your self-managed GitLab. Open Project Settings → Integrations → GitLab → Comment Settings to control behavior.
When a Playwright run finishes, TestDino posts an AI-generated summary to the merge request or commit inside your self-managed GitLab. Open Project Settings → Integrations → GitLab → Comment Settings to control behavior.
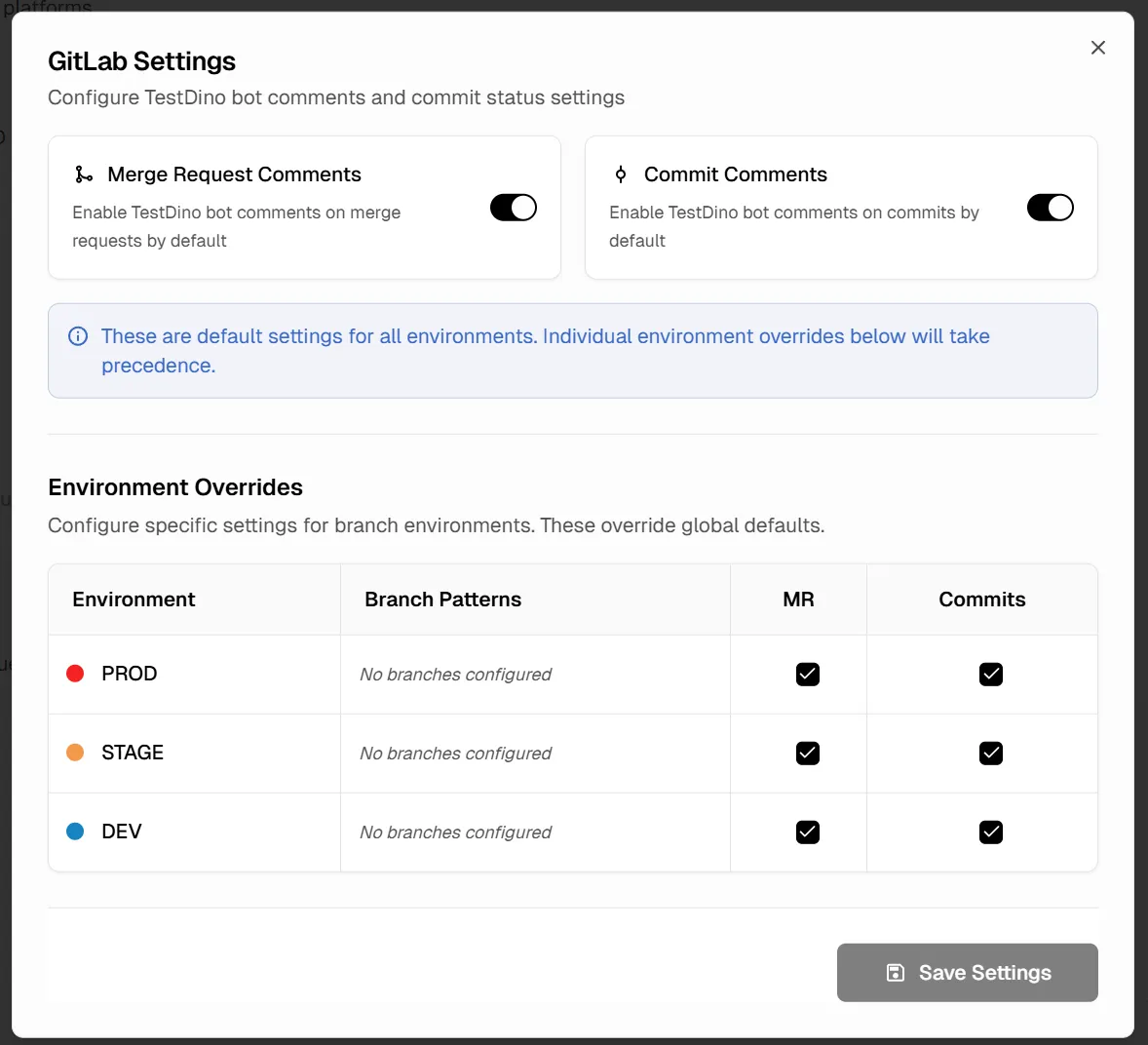
Default comment toggles
Two toggles control the global defaults:- Merge Request Comments: posts a summary to every MR on a mapped branch
- Commit Comments: posts a summary to every commit on a mapped branch
Per-environment overrides
The Environment Overrides table lists each environment configured in your project (e.g., PROD, DEV, MAIN, QA, STAGE). Each row shows:| Column | What It Controls |
|---|---|
| Environment | The environment name, configured in Environment Mapping |
| Branch Patterns | Which branches map to this environment (e.g., main, dev, staging) |
| MR | Toggle MR comments on or off for this environment |
| Commits | Toggle commit comments on or off for this environment |
Security
| Protection | Detail |
|---|---|
| Encrypted secret storage | Your OAuth Application Secret is encrypted at rest with AES-256-GCM before storage |
| Short-lived access tokens | Tokens are refreshed automatically. You never share a long-lived personal token with TestDino |
| Clean disconnect | Disconnecting from TestDino wipes the stored OAuth tokens and application credentials |
NoteTestDino stores only the metadata it needs to post comments (project ID, MR IDs, commit SHAs) plus encrypted OAuth tokens. It does not mirror your source code or CI artefacts.
Manage the Connection
View connection status
Project Settings → Integrations → GitLab displays the current connection state, the linked GitLab username, the instance URL, the selected GitLab project, and any recent comment errors.Disconnect
Click Disconnect on the GitLab card. TestDino performs two actions:- Deletes the stored OAuth tokens and application credentials.
- Stops posting comments.
Troubleshooting
Unable to reach GitLab instance
Unable to reach GitLab instance
TestDino cannot resolve or connect to your instance URL.
- Confirm the URL is correct, uses HTTPS, and is publicly reachable
- Check with your infra team whether TestDino’s outbound traffic needs allowlisting
- Confirm the TLS certificate is valid and signed by a public or internal CA
Invalid application credentials
Invalid application credentials
The Application ID or Secret is wrong, or the app was deleted on your GitLab.
- Re-create the OAuth Application in GitLab (Step 1) and enter the new ID and Secret in TestDino
- Make sure Confidential was checked when creating the app
Redirected to GitLab but got a 404 or redirect error
Redirected to GitLab but got a 404 or redirect error
The Redirect URI on the GitLab OAuth app does not match TestDino’s callback.
- In your GitLab Application, set the Redirect URI to exactly
https://app.testdino.com/api/integrations/gitlab/oauth/callback - No trailing slash, no extra path segments
Connected, but comments never appear on MRs
Connected, but comments never appear on MRs
The MR source branch does not match the branch test runs are reporting on, or comments are disabled.
- Confirm test runs send the correct branch name in metadata
- Verify the global comment toggle is enabled in Project Settings → Integrations → GitLab → Comment Settings
- Check the connecting user still has Developer access or above on the GitLab project
Comments stopped appearing after working fine
Comments stopped appearing after working fine
The OAuth app secret was rotated on GitLab, or the connecting user lost repo access.
- Reconnect via the TestDino UI using the current Application ID and Secret
Self-signed TLS certificate on your GitLab
Self-signed TLS certificate on your GitLab
Self-signed certificates are not supported today.
- Use a valid public or internal-CA-signed certificate
- Contact TestDino support about your environment if you need a different arrangement
FAQ
Do all my team members need to do this?
Do all my team members need to do this?
No. One TestDino admin connects once per TestDino project. Every team member then benefits from comments automatically.
Does the OAuth Application need to be instance-wide?
Does the OAuth Application need to be instance-wide?
No. A user-owned application works. An instance-wide application is useful only if many TestDino projects across your org connect to the same GitLab and you want centralized management.
Can one TestDino workspace connect to both Cloud and Self-Managed?
Can one TestDino workspace connect to both Cloud and Self-Managed?
Yes. Each TestDino project chooses its own GitLab connection independently.
How do I revoke TestDino's access entirely?
How do I revoke TestDino's access entirely?
From TestDino, click Disconnect. From GitLab, go to User Settings → Applications → Authorized applications and revoke TestDino there as well.
GitLab Cloud Integration
Connect TestDino to gitlab.com via OAuth for MR comments and sync
Environment Mapping
Map branches to environments for targeted comment routing
Pull Requests Dashboard
View all MRs with test run results, trends, and AI insights
Node.js CLI
Install and configure the TestDino CLI